Recently, I came across use case where applications are being deployed using AWS Beanstalk Services. When you deploy your applications using Beanstalk, your application URL looks like my-environment.us-west-2.elasticbeanstalk.com, which is not at all user friendly. Beanstalk details
To make the URLs user friendly, one must Launch Reverse proxy server (EC2 instance). After launching server, create DNS (Forward look up) record entry in our existing domain under your parent domain and point to Reverse Proxy Server. The approximate cost of server is $79/ month & additional certificate cost. Also, this is the single point of failure.
Requirement
Host a sub-domain(demo.example.com) of existing domain(example.com) on Route 53 Read more, while the rest of the domain remains with existing service provider.
This can be done by doing a delegation of authority for the sub-domain alone to Route 53. Sub-domain delegation is done by creating a record type of NS and the data of the record type are the name-servers that will contain the DNS records for the sub-domain.
Pre-requisite
Following are important pre-requisites
- One must have AWS Account to host the subdomain and launch applications
- There must be domain registered with any of the service provider.
- SSL Certificate (optional)
Architecture
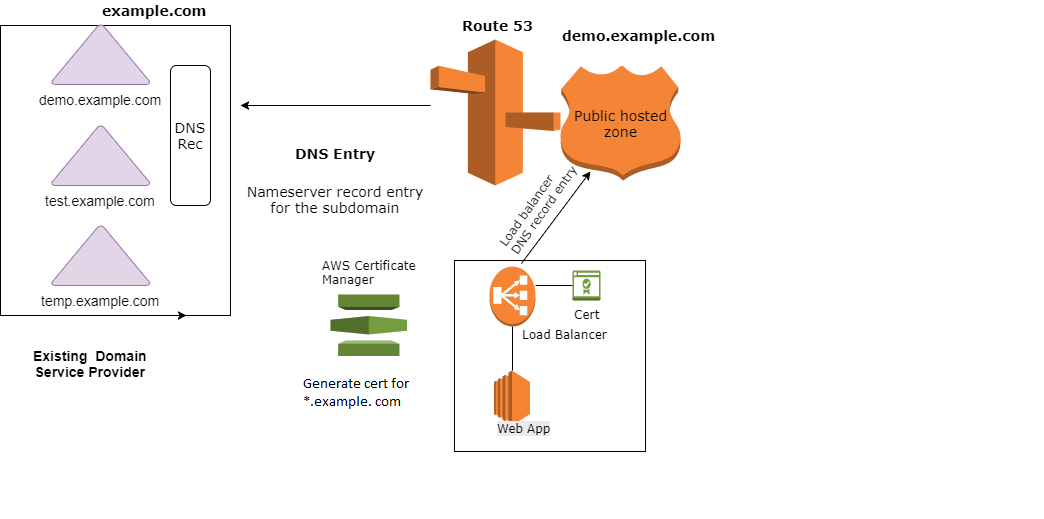
Steps to perform
- In AWS Route 53 console, create a public hosted zone with the name of the sub-domain that you want to host in Route 53. Here I have example.com domain hosted on GoDaddy. I want to create example.com subdomain in my parent domain
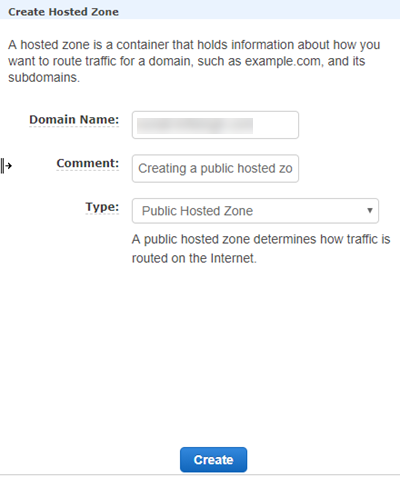
Route 53: Create subdomain as a hosted zone on R53 - After creation of the hosted zone, 4 nameservers & 1 SOA DNS record is generated for that hosted zone
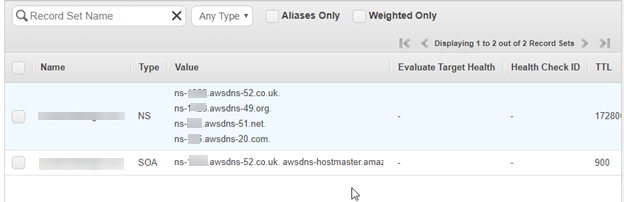
NOTE: Keep note of these Nameservers. We will require them for later use
- The next step is to do the delegation in our existing Service provider account. Create a subdomain(example.com) with the same name that we have created on Route 53
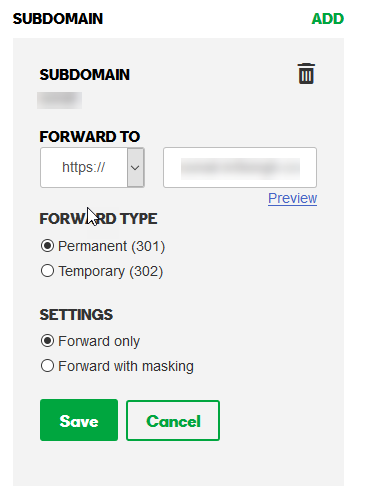
Registering the newly created subdomain with the parent service providers - Now, Create DNS record entries for newly created subdomain. Use 4 nameservers, which were generated in Route 53 as the values for the NS record. Make sure the record type is NS.

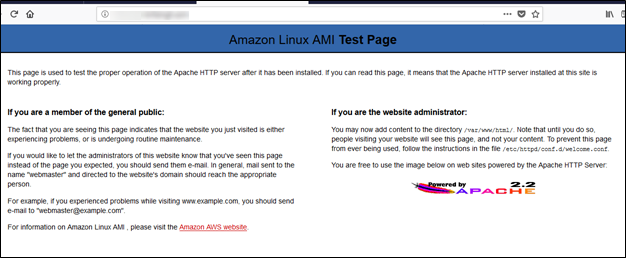
Route 53 NameServer record entries - We have configured it successfully. Now, we will do the testing by launching a beanstalk Web application. please check how to launch the Beanstalk application. Put this application behind load balancer.
- Create a DNS record in Route 53 which points to the Load balancer (Web Application is running behind load balancer). Below screenshots refers to DNS record entry(secelb.demo.example.com) in Route 53
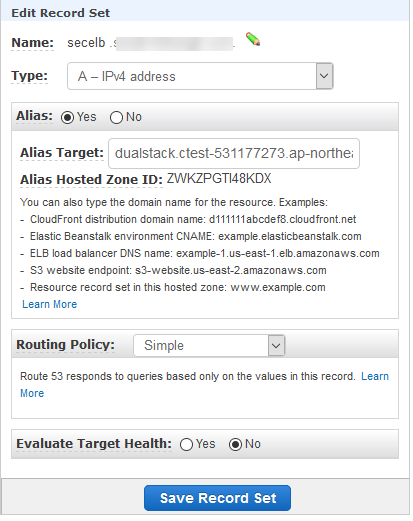
DNS Record Set entry on Route 53 - Open that subdomain in the browser
We have successfully hosted the subdomain in Route 53. Now, we will create the SSL certificates for all the application URLs in our domain using AWS Certificate Manager.
- Go to AWS Console and Select AWS Certificate Manager service
- If we want to generate a certificate for the domain in Certificate manager, use option Request a certificate. You already have certificate for your domain choose Import a certificate option.
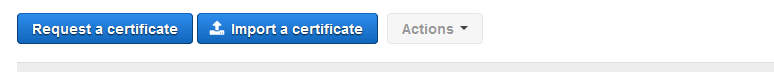
AWS ACM console dashboard - Choose option “request a public certificate “
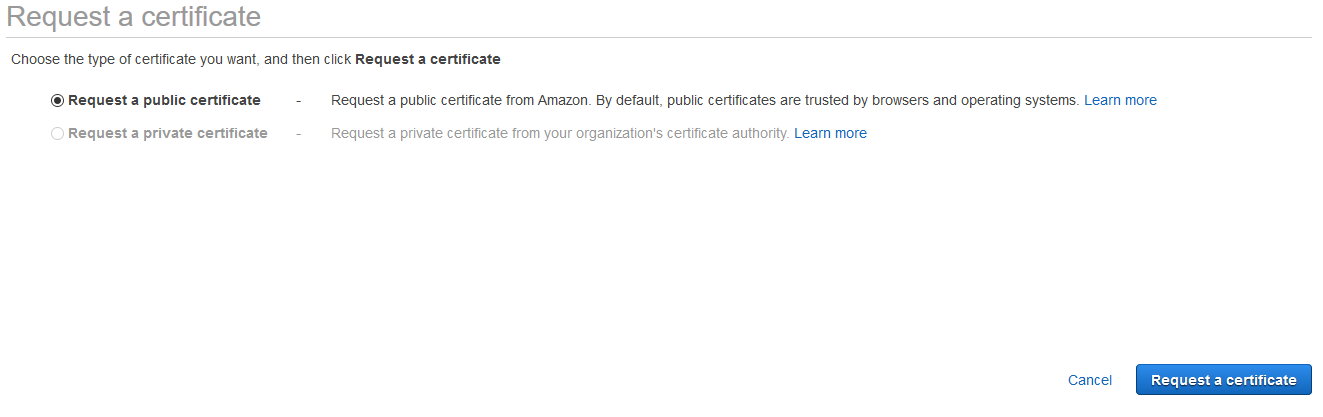
Generating Public Certificate - Add the domain name. Also, we can specify the ‘*’ to create wild card certificate.
So, I have added example.com & *.example.com

Registering domain name - Choose Email validation method to validate your request. It will send a confirmation email on administrator email account for approval

- Review your request
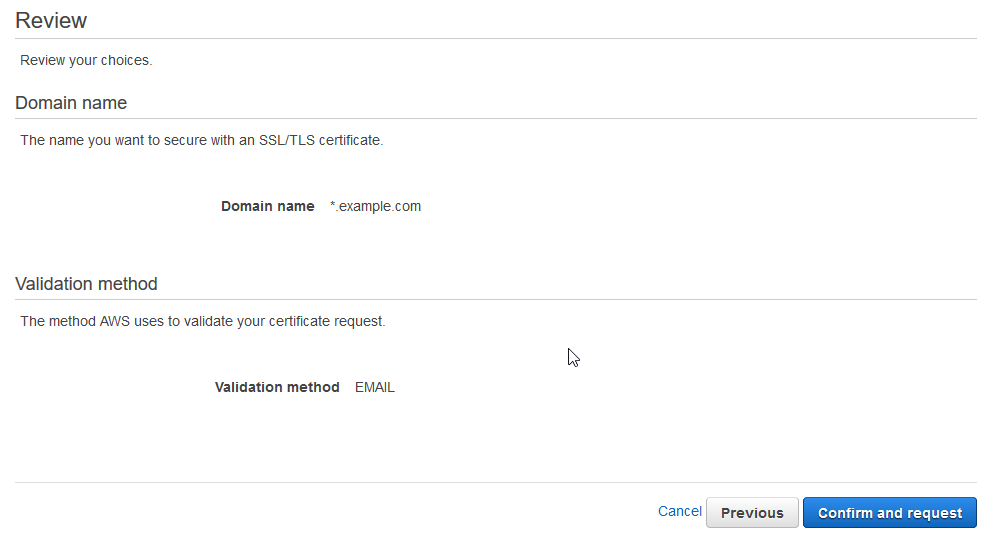
- Once you confirm your request, it will show the status as “pending validation”
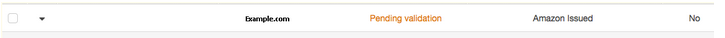
- It sends email to the domain name you specify in the Domain-name parameter or in the optional Validation-domain You need to click I Approve link in the email.
- administrator@your_domain_name
- hostmaster@your_domain_name
- postmaster@your_domain_name
- webmaster@your_domain_name
- admin@your_domain_name
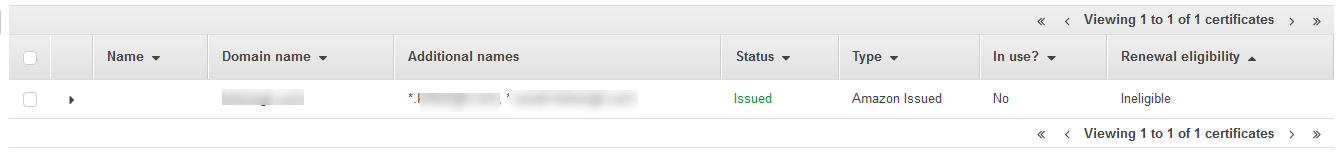
- You can navigate back to the ACM console. After validating the domain name, ACM changes the validation status to Success. After AWS issues the certificate, ACM changes the certificate status to Issued
- Now attach this certificate to load balancer. Click Listeners. Click Edit. Add HTTPS port
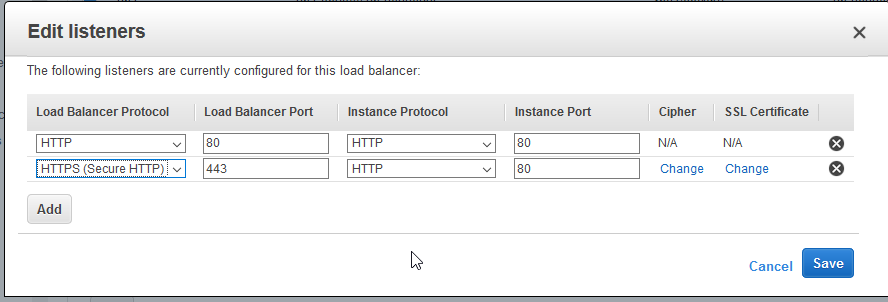
Open listener port 443 on the load balancer - Click change SSL Certificate option. Choose ACM option from pop up. Select the certificate.

Choose the ACM certificate in Load Balancer configuration - Click change Cipher option. Choose “Predefined Security Policy”
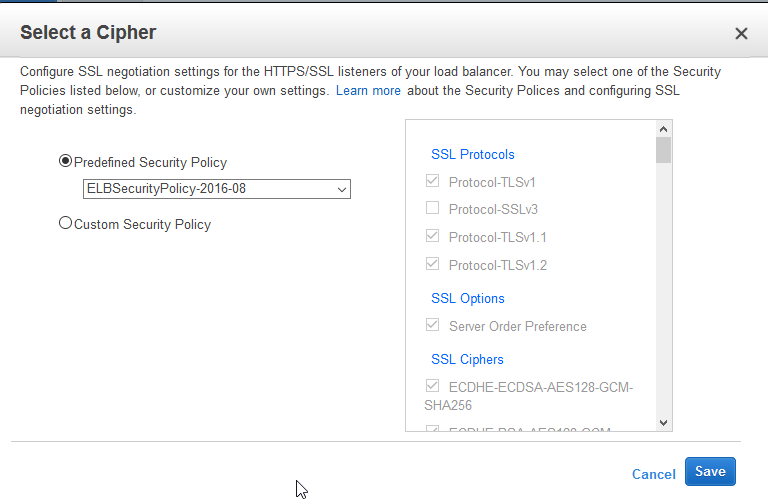
Selecting the default Load Balancer cipher
Note: Make sure port 443 is open on Server as well as on Load balancer.
- Click change SSL Certificate option. Choose ACM option from pop up. Select the certificate.
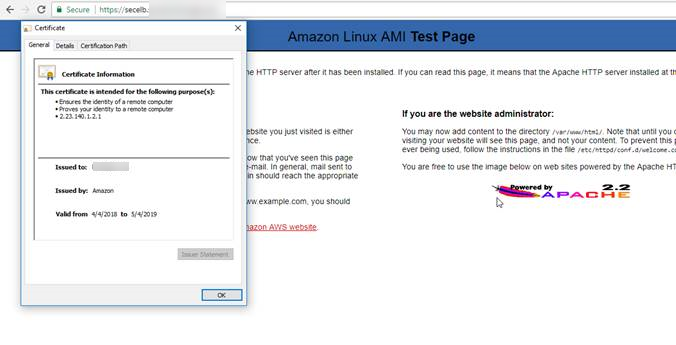
- After this configuration, Load balancer will take some time to propagate the certificate. Keep checking in browser. Open the domain(secelb.demo.example.com) in the browser.
Conclusion
Today, we have seen how to host a sub domain in Route 53 (which AWS service to host domains)
Create SSL certificate using AWS certificate manager service and apply it on Load balancer.
Next, we will see how to import the existing certificate in AWS Certificate manager and apply it on Load balancer.
Contributed by : Sonali Shah
https://www.linkedin.com/in/sonali-shah/
Reference
https://docs.aws.amazon.com/acm/latest/userguide/gs-acm-validate-email.html
https://docs.aws.amazon.com/acm/latest/userguide/import-certificate-format.html
https://docs.aws.amazon.com/acm/latest/userguide/import-certificate-prerequisites.html